 )
or unlocked (
)
or unlocked ( ).
If it is locked, you will be prompted for the master password when you
try to restore it.
).
If it is locked, you will be prompted for the master password when you
try to restore it.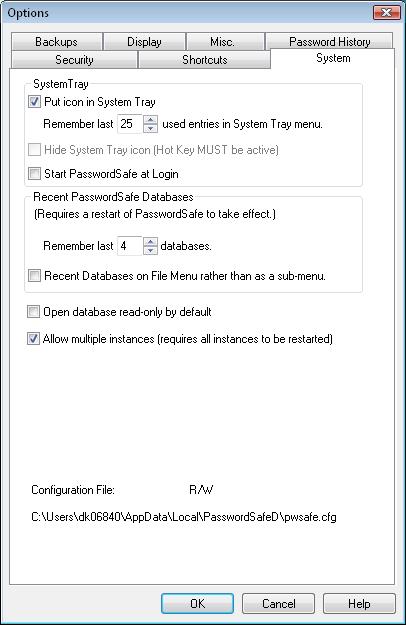
The System Tab provides access to settings that are related to Password Safe's interaction with the system on which it is running.
If checked, Password Safe will minimize to the System Tray area. If unchecked, the program will minimize to the task bar.
The icon in the system tray indicates whether the password database is locked
( )
or unlocked (
)
or unlocked ( ).
If it is locked, you will be prompted for the master password when you
try to restore it.
).
If it is locked, you will be prompted for the master password when you
try to restore it.
If the Put icon in System Tray option is enabled, you can right-click on the system tray icon to get to the most recently used entries directly, without going through the application's main screen. This option allows you to configure how many recent entries you wish to keep in the system tray icon's list. NOTE: This list is saved in the database only when a read/write database is saved or closed.
If checked, this will cause Password Safe to hide his icon in the system tray. This functionality will only be enabled if the Hot Key to start or reopen Password Safe is active.
If checked, this will cause Password Safe to start automatically in the System tray when you log on. Note that you will be prompted for the master password the first time you double-click on the System Tray icon, not before.
These controls allow you to configure how many recently opened databases are displayed in the File menu. Note that you need to exit and restart Password Safe for changes in this control to take effect.
This option determines how the recently opened databases are presented in the File menu - directly on the menu, or as a sub-menu.
Setting this option will cause Password Safe to open databases in read-only mode by default. This may be useful in a multi-user environment, as by default Password Safe allows write access to the first person who opens the database, and restricts others to read-only mode. With this option, you can determine by site policy who will have write-access to a given database.
Prior to version 3.05, Password Safe used the Registry to store configuration data, such as non-default options settings, last database opened, etc. As of this release, this information is split into database-specific and user/machine specific settings, with the latter being stored in a separate configuration file. Selecting this option and clicking on the Apply button will cause the registry settings to be cleared. This is useful if you wish to remove traces of Password Safe on your PC. Note, however, that this means that older versions of Password Safe will revert to default value for some of the settings.
Notes:
Prior to version 3.22, Password Safe kept application preferences (such as some
of the user options, last files opened, window size and location, etc.)
in a file in the same directory as the Password Safe executable. This
has caused problems with recent versions of Windows when users were not
given write access to this directory. Therefore, as of version 3.22,
the configuration file (pwsafe.cfg) will be created in the standard
location for such files (in the user's 'Application Data' directory).
By default, upgrades to existing installations will not change the existing preference file ("if it ain't broke, don't fix it"). However, if a user wishes to switch to the new setting manually, selecting this checkbox and clicking on 'Apply' will do so.
In more detail: The configuration file is designed to support multiple users from multiple machines. The migration function will move the current user's settings (associated with the current PC) from the configuration file to the new location. If there are other user/machine specific configurations in the file, they will be left untouched. If, on the other hand, there are none left after migration, the empty file will be deleted.
If you wish to share a common configuration file between users and/or across different PCs, you can either keep the file in the executable directory, or specify its location explicitly using the '-g config-file' option, as described in command line arguments.